Here’s A Quick Way To Solve A Info About How To Start Sniffer
Then use ctrl+c to terminate the same.
How to start sniffer. Then, you install the program and launch it. Add used panties and other items to my store. Start up your favorite browser (ceweasel in kali linux).
I want to achieve this using python script. First, you download it on your computer. Overview on how snifffr works.
Start up the wireshark program (select an interface and press start to capture packets). [admin@mikrotik] tool sniffer> save file. It's actually a very simple fix, takes a few minutes.
Register the medium speed can bus in the vehicle's profile. By selecting the default options, the linux sniffer starts capturing packets. You can open the configuration window by clicking the config button in the program, and check the option automatically run msn sniffer when i log on to windows.
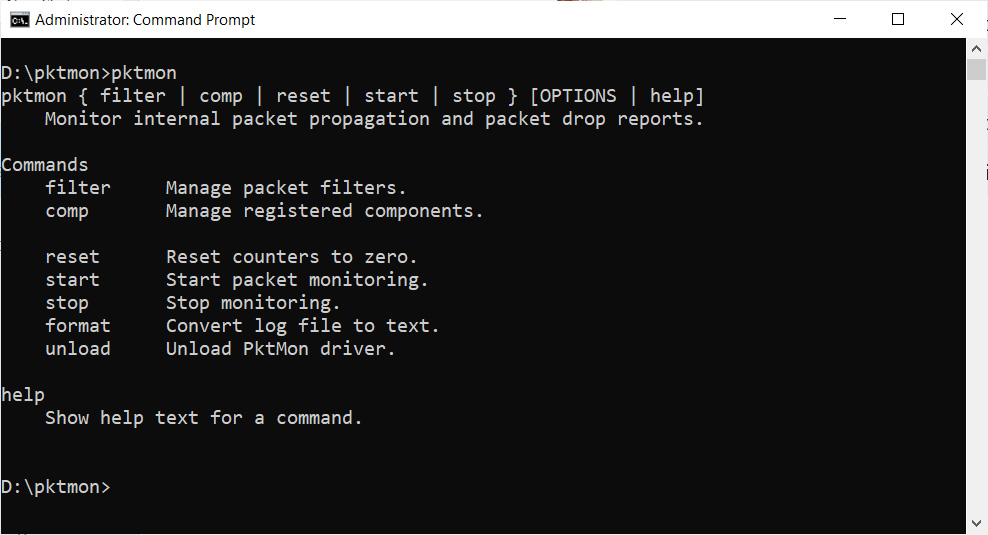
Initialization when the user starts the sniffer, a new instance of the class jade.tools.sniffer.sniffer is created:. Unlike tcpdump, iptraf will track every tcp connection in the top window and will scroll all udp. [admin@mikrotik] tool sniffer> start [admin@mikrotik] tool sniffer> stop below the sniffed packets will be saved in the file named test:
Wireshark will continue capturing and displaying packets until the capture buffer fills up. Today i'll be showing you guys how to fix your cain and abel sniffer problem on windows 10. Telling the ams to sniff an agent when the user.
In your browser, go to wayne state. Search for jobs related to start sniffer or hire on the world's largest freelancing marketplace with 21m+ jobs. (that way we can use it in the next steps).
To start the packet capturing process, click the capture menu and choose start. Fill out your profile details. Once the connection is complete, right click on.
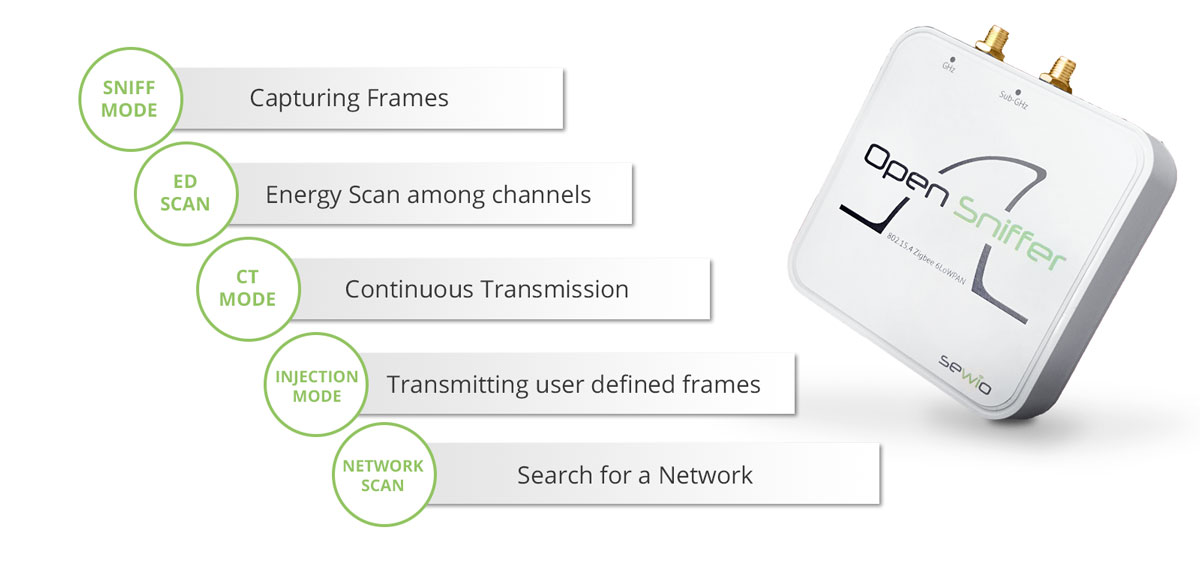
Therefore, as defined in our cybersecurity glossary, a packet sniffer is a type of software designed to monitor and record traffic on a network. 1) connect your node to an insight adapter. It can be used for good, to run.
Sniffer software is used for ethical reasons, such as when a network administrator analyses network traffic flow.